Cybersecurity researchers have discovered a large malware campaign that uses fake GitHub tools to distribute a dangerous data-stealing malware called BoryptGrab. The attackers are taking advantage of the trust people have in open-source platforms and free software downloads.
Many users search online for tools such as game cheats, media applications, or productivity utilities. Cybercriminals are exploiting this behavior by creating fake GitHub repositories that appear legitimate but actually deliver malware.
Researchers have already identified more than 100 public repositories connected to this campaign. These repositories often include popular keywords to rank higher in search results, making them easier for victims to find. Some repositories also contain Russian-language comments and code patterns, suggesting that the operation may be linked to Russian-speaking threat actors.
How the Fake GitHub Malware Campaign Works
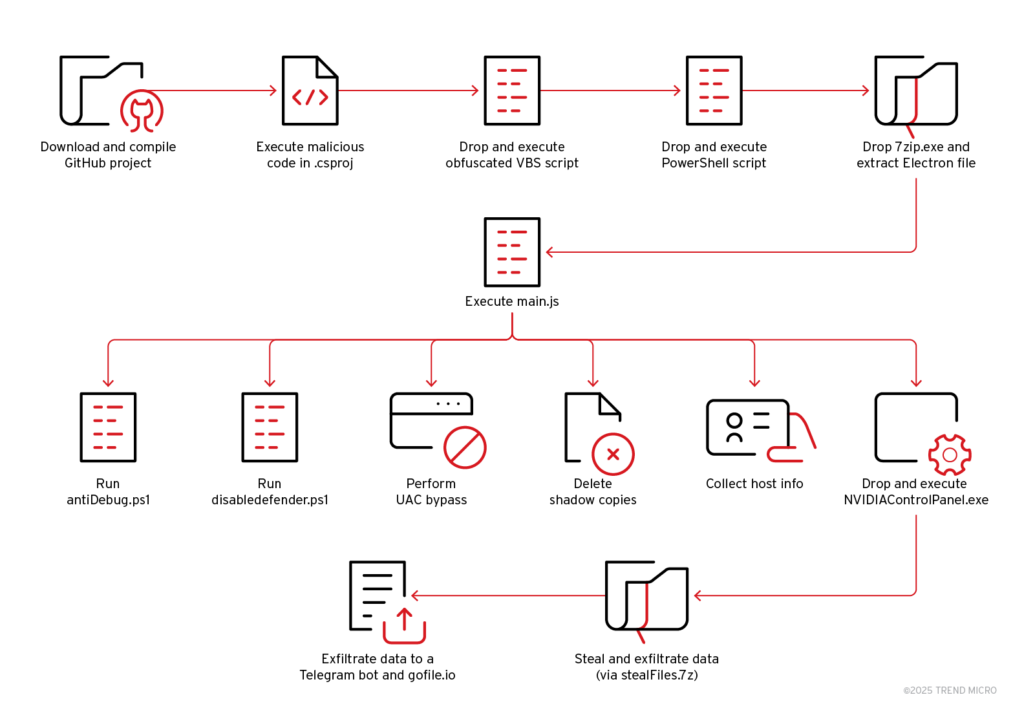
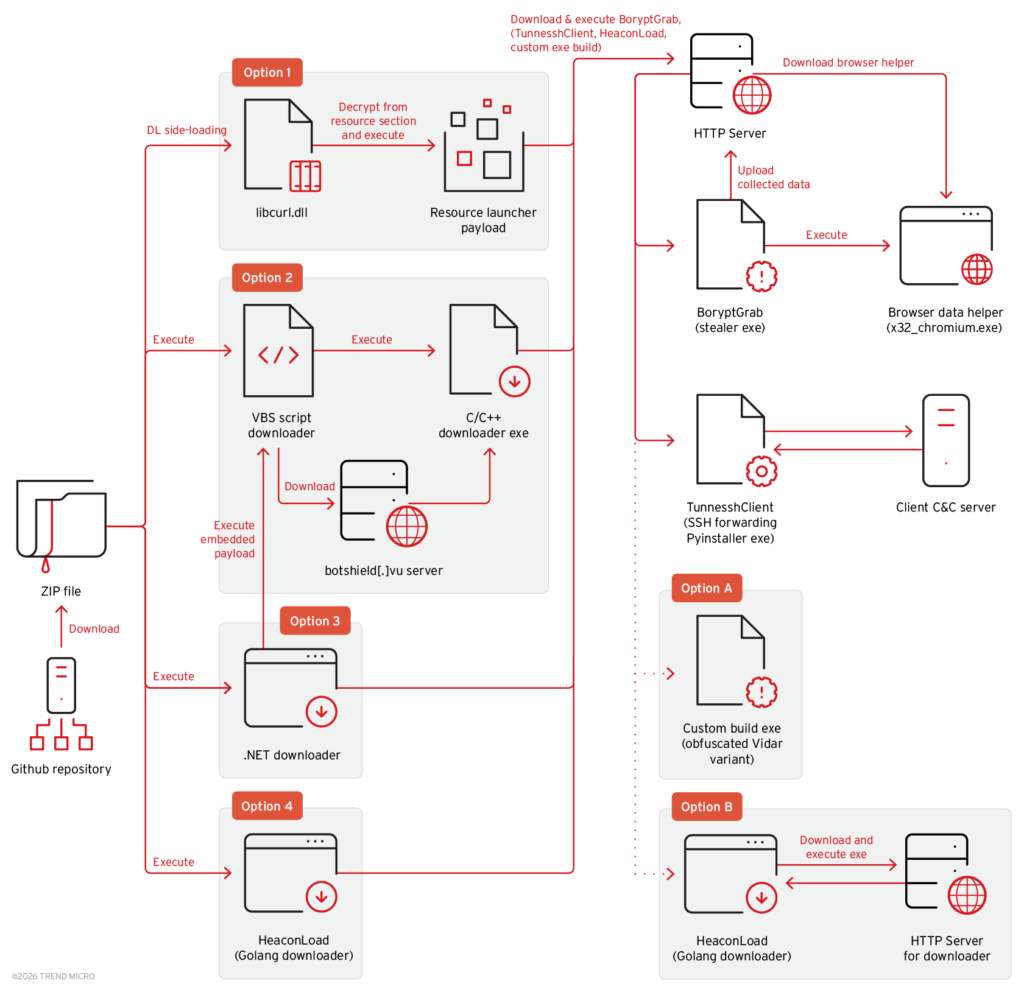
The attack begins when a user downloads a ZIP archive from a GitHub repository that appears to contain a useful program.
Once the file is opened, the malware chain starts. Some archives include executable files that use DLL sideloading to run hidden malicious code. Other versions contain a VBS downloader that runs obfuscated PowerShell commands to fetch additional malware from remote servers.
In certain cases, the malware attempts to add Microsoft Defender exclusions, which reduces the chances of detection by security tools.
After the initial infection, the attack may install several additional malware components. Each component has a different role in the attack process.
| Malware Component | Function |
|---|---|
| BoryptGrab | Main data-stealing malware |
| Vidar Variant | Secondary information stealer |
| HeaconLoad | Downloader used to fetch extra payloads |
| TunnesshClient | Backdoor that creates reverse SSH tunnels |
This layered structure allows attackers to deliver different payloads to different victims, making the campaign more flexible and harder to detect.
BoryptGrab Targets Browsers and Cryptocurrency Wallets
The primary goal of this campaign is data theft. BoryptGrab is a C/C++ based stealer designed to extract large amounts of information from infected systems.
The malware targets several popular web browsers, including Chrome, Edge, Brave, Opera, Firefox, Vivaldi, Chromium, and Yandex. It can steal saved passwords, browsing information, and other stored credentials.
BoryptGrab also focuses heavily on cryptocurrency wallets, which makes the attack particularly dangerous for crypto users.
Some of the targeted wallets include:
- Exodus
- Electrum
- Ledger
- Trezor
- Atomic Wallet
- Binance Wallet
- Wasabi Wallet
- Bitcoin Core
- Ethereum wallets
In addition to wallet and browser data, the malware can also capture screenshots, Telegram and Discord information, system details, and files stored in common folders.
Once the data is collected, it is compressed and sent to servers controlled by the attackers.
Why This Threat Is Growing
This campaign shows how cybercriminals are combining several techniques to scale their attacks. These include search engine optimization abuse, fake GitHub repositories, modular malware loaders, and crypto wallet theft tools.
Because the repositories appear legitimate and are hosted on a trusted platform, many users may not suspect anything unusual.
To stay safe, users should always download software from verified sources, carefully review GitHub repositories, and avoid installing unknown tools from public projects.
The rise of campaigns like the BoryptGrab malware operation highlights the growing risks associated with downloading free software from untrusted sources. Being cautious while downloading files online is one of the most effective ways to protect personal data and digital assets.